How To Secure A Data Center
A data center consists of groups of networking and computational equipment that process and store information for a business in a central location. To keep it secure, businesses must employ both virtual and physical systems designed to protect the data center. In addition to protecting the organization’s computational assets, specific network security measures must be implemented to prevent malware attacks and other threats from penetrating the data center.
Physical security
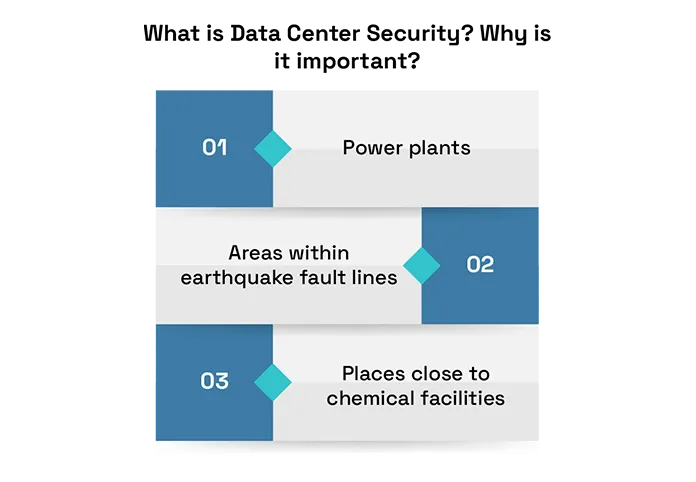
Choosing the right location should be a primary focus when building a data center. Certain areas must be avoided because they present security and safety risks that can cause service interruptions or complete failures. These include:
Power plants
Areas within earthquake fault lines
Areas where airplanes cross as they land
Places close to chemical facilities
Locations where hurricanes are common
Places likely to experience tornadoes
Areas prone to seasonal wildfires
Areas exposed to flooding
Besides building above floodplains, using thick concrete walls may also provide an extra layer of physical security. Concrete walls a foot thick or thicker can help prevent natural disasters and even explosions from impacting a data center’s physical security.
Virtual or software security
Virtualization technology is common in data center technology. With virtualization, a business gets a digital infrastructure that supports or mimics its primary systems. This enables administrators to manage the data center’s services from remote locations. It also allows for greater flexibility because software can be used to manage the security and workflows of the data center. Some data centers take advantage of virtualization to set up access to public cloud services, while others incorporate it in their internal data center. While the use of software and cloud solutions, like SoftLayer and Amazon Web Services (AWS), provides administrators with more flexibility, it also exposes the data center’s assets and systems to cyber threats. In some data centers, security is part of the services offered to the businesses they serve. Some common measures include intrusion prevention and detection systems, firewalls, and next-generation firewalls (NGFWs). An organization’s IT administrator can use these measures to dictate who is allowed access to the data center’s resources in general, or who can access certain sections of the network. Two-factor authentication (2FA) can also help an organization secure its data center resources. This involves users proving their access privileges by using something they know, like a password, in combination with something they physically have, like a phone or flash drive.
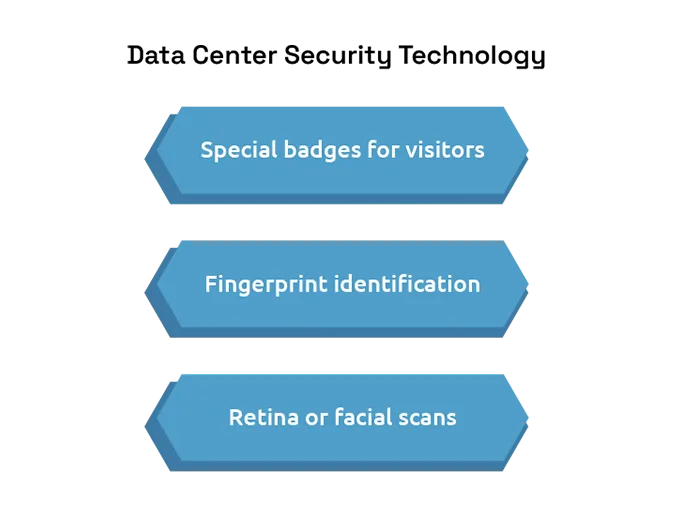
Data Center Security Technology
Only the most recent technologies will be sufficient to maintain the security of a data center Because many—if not all—of the assets within may be critical to a business’s operation, you need up-to-date security measures to protect them from the ever-evolving threat landscape.
Multi-factor authentication
With multi-factor authentication (MFA), you automatically get an extra layer of security, particularly because at least two elements are used to validate access rights. If an attacker is to obtain one authentication measure, they still need to find a way to get the second before too much time goes by and the login session either times out or a security alert is generated.
While this is common when securing digital assets in a variety of situations, it is also a powerful security solution to ensure that only authorized individuals can access the physical areas of a data center. Some requirements to access data center equipment can include:
A complete check-in process that requires government-issued identification
Special badges for visitors
Fingerprint identification
A physical key that can provide access to areas where equipment is run or stored
Badge key cards, which can be verified before going through doors between sensitive areas
Retina or facial scans
Surveillance monitoring systems
Surveillance monitoring ensures high security for a couple of different reasons. First, you can record who enters which areas, as well as what they do once inside. This information can be reviewed if there is a breach to track down the attacker. Second, the presence of security monitoring systems can be a powerful deterrent against attackers. Knowing they have to find a way to bypass a camera system can be enough to encourage them to move on to a softer target.
A surveillance monitoring system is a more powerful asset when it is operated by human personnel. While a digitally based system that is always on may be effective in some situations, a human running a surveillance system can be a more powerful impediment. In addition, a security professional can provide suggestions on how to maximize the effectiveness of the surveillance system. Also, the system may need improvement at times, and the ability of an individual to pinpoint areas of improvement can be invaluable.
Redundancy
Redundancy is a key component of data center resiliency. With redundant elements in place, if the primary component malfunctions or breaks down completely, the secondary component can be activated automatically or manually, and key systems can maintain their function.
For example, the power system needs to have a redundant backup, as do other crucial components. These may include:
The cooling system, which keeps servers from overheating while processing data
Electricity is used to power specific areas of the data center, such as those housing servers or key
networking components
Network connections that provide information throughput to business-critical systems
Redundancy can also play a key role in making sure downtime is reduced when servers malfunction, or even to maintain uptime in virtual systems. For example, a data center, for some processes, may run two servers in parallel, both using the same operating system, security measures, and software. If one is to go down, the other can automatically turn on, maximizing uptime for users.
Redundancy can also be used to tighten the data center’s digital security. In many cases, when two components are working in tandem for digital security, they are both redundant and complementary. For example, multiple firewalls can be set up at different points within a network, one at the outer edge and another between the edge and a server. The two firewalls are redundant because they may catch many or all of the same threats. However, you can use the edge firewall to inspect the outgoing traffic that gets past the firewall in front of the internal server. With this data, you gain insight into the existence of internal vulnerabilities, as well as how threats that exploit the vulnerabilities behave.
Redundancy is also a valuable strategy when it comes to the data center’s network infrastructure. The data center can take advantage of two internet service providers (ISPs), for instance, with one only being used when the other goes down. The traffic from both ISPs can be run through a high-throughput firewall to ensure continuity if the primary provider’s signal fails or has to be shut down due to a security breach.
Conclusion:
Data center security is essential for protecting critical data, systems, and infrastructure from physical and cyber threats. As businesses depend more on digital operations, strong security measures help ensure uptime, data privacy, and trust. Investing in complete security is not just smart, it’s necessary for long-term success.